Cybersecurity – Industry 4.0
By Gurmeet Singh

Since the beginning of the pandemic, the FBI has seen a fourfold increase in cybersecurity complaints, whereas the global losses from cybercrime exceeded $1 trillion in 2020. World Economic Forum’s “Global Risks Report 2020” states that the chances of catching and prosecuting a cybercriminal are almost nil (0.05%). Given the circumstances, business awareness and resilience are key to securing sensitive data and avoiding breaches.
Cyber threats are getting more sophisticated and intense amid the increasing levels of remote work and dependence on digital devices. The recently concluded Joe Biden – Putin summit in Geneva had a special focus on addressing the increased incidence of cyberattacks that are most important today in the fast-paced technology dependent industries. The wars of today and tomorrow would be fought in the cyberspace rather than by bullets on the ground. The complexity of business is growing by the day and with it we see the growth of crimes in various industry verticals.
The cyber risks across supply chains in almost all infrastructure sectors, including healthcare and food, whose assets, systems and networks are so vital that their incapacitation or destruction would have a debilitating effect on various platforms. The recent ransomware attacks, including attacks on the colonial pipeline and JBS Meat Packers, have demonstrated the risk posed by cybercrime to the critical infrastructures, the business economics and all-important public safety that gets compromised.
As far India situation is concerned and as reported by the Sophos Survey in March 2021, about 52% of domestic companies fell victim to a cyberattack in the preceding 12 months. The cyberattacks surged 3-fold to 1.16 million in 2020. On an average approx. 3137 cyber security-related issues were reported every day during 2020
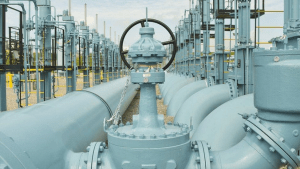 On May 7, hackers launched a ransomware attack on an American oil pipeline system that carries petrol and jet fuel, forcing it to halt operations. Spanning nearly 9,000 km between Texas and New York, the Colonial Pipeline is the largest pipeline system for refined oil products in the US.
On May 7, hackers launched a ransomware attack on an American oil pipeline system that carries petrol and jet fuel, forcing it to halt operations. Spanning nearly 9,000 km between Texas and New York, the Colonial Pipeline is the largest pipeline system for refined oil products in the US.
The attack on it was “probably the most significant ransomware attack on one of our critical infrastructures ever,” said John Katko, US Representative for New York’s 24th congressional district. Within hours, the Colonial Pipeline Company — with the help of the FBI — paid the hackers the 75 bitcoin ($4.4 million at the time) ransom they had demanded.
On receiving the payment, the hackers gave the company a decrypting tool to restore its computer network. But the tool was so slow that the company continued using its own backups to restore the system, Bloomberg reported.
Though the most egregious, the attack on Colonial Pipeline was hardly unique. In the past two years ransomware attacks have become frighteningly commonplace. There were seven ransomware attacks in the US every hour during 2020, targeting individuals, businesses and — increasingly — vital infrastructure.
Cyber Attack: Industry 4.0 – Pharma 4.0
We have all witnessed the importance of digitization and the strides that the industry is making irrespective of any sector in transforming from paper logs to digitization in operations. These are for various reasons including data integrity and enhancing operational excellence. Pharma sector remains in the forefront of all such efforts as there is large data that is handled in product development, new molecule development, the clinical trials which go over various phases and securing all these and getting to a logical conclusion of analysis and testing procedures.
Cyber Attack and Pharma
The current times have shown how technology has been an enabler as well as a determinant factor in the effectiveness and efficiency of our systems and procedures. Now, what is a cyber attack? A cyber attack is an assault launched by cybercriminals using one or more computers against single or multiple computers or networks. A cyber attack can maliciously disable computers, steal data, or use a breached computer which may lead to other attacks. Cybercriminals use a variety of methods to launch a cyber attack, including malware, phishing, ransomware, denial of service, among other methods.
Cyber Proof Your Enterprise with Security
The Covid-19 pandemic also hastened the cyber pandemic and we need to recognize that this cyber pandemic is already here and hitting the corporates hard. Even the governments across the world have been impacted by work disruptions and also data leakages, which will have a sizeable financial impact and other adverse long term business implications. Over 99% of all organizations today are not protected against cyber attacks. Even as we speak, the skill set available to counter these cyber attacks in the world is a minuscule number as compared to what is required in terms of skilled manpower resources and of course the infrastructure to combat the growing menace of such attacks.
The global shortage of cybersecurity professionals exceeds 4 million today, and the global cybersecurity workforce must grow over 150% annually to meet the demand for skilled cybersecurity talent. While pharma companies may be strategic about attracting and retaining quality cybersecurity talent, people with such skills will be scarce in the near term thereby making it difficult to fill the gaps.
The proficiency of the cyber attackers or the hackers lies in the fact that all such cyber attacks and threats are designed in such a manner that these avoid detection for a long period and by the time it hits the company’s IT systems, it would have been too late.
The Threat of Cyber Attacks is Real
In 2020 when the pharma companies had been involved in the race to get the coronavirus vaccine to market, the threats of cyber attacks were on the rise. In July 2020, cybersecurity agencies and authorities in the UK and Canada released a joint warning of attacks targeting Covid-19 research and vaccine development facilities. The concern is that such attacks could cause delays in delivering vaccines, which has the potential and has impacted the speed of delivering the appropriate solutions and in the process losing valuable human lives.
Insider Threats
One of the largest risks that any industry faces including the pharma companies is the threat from inside the organization. The employees within exhibit various behaviours and are most difficult to track. Such aberrations may be an outcome of frustration, intra and inter-department rivalries competing to earn recognition and or make money by selling classified research or customer data, etc. Even in some cases a well-intentioned employee may go in for shortcuts and in the process sidestep SOPs to save time to gain some browning points.
Regulatory and Compliance Requirements
Historically speaking the pharmaceutical companies have made various security efforts on meeting GMP and SOP compliance requirements. However, the requirements have become more and more complex by the day and the challenge lies in integrating the various modules and infrastructure in such a manner that the track and trace and audit trails are well established and verifiable in real-time. The issue today which confronts most organizations is the struggle they have to demonstrate GMP/ SOP compliance.
Enhanced Use of Tech Devices, Digital Solutions & WFH
The partial implementation of digital solutions not very well integrated is also contributing to a greater number of ‘attack targets’ in pharma companies including the cloud migrations vs on-premise solutions backed with a huge surge in remote work. The alarming cybersecurity statistics for 2021 and various cyber attacks that have taken place is an emergent situation and a call to action for all company leaders around the world to recognize and give maximum importance to risk management.
Solutions and way forward
The IT security solution providers offer the entire bouquet of services:
- Fully integrated end to end secure solutions
- Pharma space – solutions focussing on GMP and regulatory compliances
- Track and trace enabling smooth and visible audit trails
- Systems – preventive with multiple layers of firewalls and security arrangement
- Ensure data protection, data leakage, and data integrity
- Robust systems to keep off data piercing attempts by hackers
- Network security and cyber attack vigilance and governance
The solution lies in looking for an integrated and comprehensive architectural approach to network security. Such an approach provides the automation, visibility, and fast response to threats that are in compliance with the regulatory requirements and also defeat the attackers.
Read more at:https://www.cxotoday.com/columns/seven-cybersecurity-challenges-plaguing-pharma-industry/
https://www.weforum.org/agenda/2021/06/joe-biden-vladimir-putin-summit-cybersecurity/
About the Author
 Gurmeet Singh is Senior Advisor Business Development with Atachi Systems Inc US and Director Pharma Networks – a veteran for over 30 years in the Indian pharmaceutical sector. He has worked with some of the best pharma companies at the decision-making levels in companies like Ranbaxy, Wockhardt-Swiss and Ireland, Orchid Pharma and Midas GmbH. He was associated in 2018 as Pharma Development Consultant with DNDi – Drugs for Neglected Diseases initiative – a Geneva based R&D organization. Mr. Singh is a Bachelor at Law (LL.B), a Post Graduate in Management Studies and Post Graduate Diploma in Intellectual Property Rights Law. He can be contacted on [email protected] and [email protected] and handset +919703599123.
Gurmeet Singh is Senior Advisor Business Development with Atachi Systems Inc US and Director Pharma Networks – a veteran for over 30 years in the Indian pharmaceutical sector. He has worked with some of the best pharma companies at the decision-making levels in companies like Ranbaxy, Wockhardt-Swiss and Ireland, Orchid Pharma and Midas GmbH. He was associated in 2018 as Pharma Development Consultant with DNDi – Drugs for Neglected Diseases initiative – a Geneva based R&D organization. Mr. Singh is a Bachelor at Law (LL.B), a Post Graduate in Management Studies and Post Graduate Diploma in Intellectual Property Rights Law. He can be contacted on [email protected] and [email protected] and handset +919703599123.
IMA Exclusive
![]() An exhaustive coverage of the world leader in the design and manufacture of automatic machines for the processing and packaging of pharmaceutical products. Wide portfolio of machines and the ability to offer tailor-made solutions to satisfy the most sophisticated requests in the market are the biggest strengths of IMA.
An exhaustive coverage of the world leader in the design and manufacture of automatic machines for the processing and packaging of pharmaceutical products. Wide portfolio of machines and the ability to offer tailor-made solutions to satisfy the most sophisticated requests in the market are the biggest strengths of IMA.









